Specialized Pen Tests Right-Sized for Your Business
Unlike many security firms, our Offensive Security Team goes beyond traditional penetration testing to deliver practical, actionable insights tied to real-world risk.
We meet you where you are, helping you choose the right test based on your security maturity, business needs, and compliance requirements—so you get an assessment that actually moves security forward.
Specialized Penetration Tests
Adversarial Simulations
Red and Purple Team engagements simulate real-world attacks and threat emulation to expose hidden gaps, strengthen detection and response, and improve security maturity through collaborative testing.
Web & Mobile App Pen Tests
We provide rigorous penetration testing of your mobile apps, web apps, & application secure code reviews s to uncover exploitable weaknesses that could expose sensitive data or enable unauthorized access.
Network Pen Tests
Internal & External network penetration tests simulate insider and internet-based attacks to identify weaknesses behind the firewall and in publicly exposed systems before attackers exploit them.
API Pen Tests
API penetration testing assesses APIs for authentication, authorization, and data exposure flaws, helping organizations secure integrations, mobile apps, and cloud services that handle sensitive information.
Device & IoT Pen Tests
Conduct comprehensive scans and penetration tests of devices with embedded software & IoT devices within your ecosystem to identify potential vulnerabilities & entry points for intrusions.
Thick/Thin Pen Tests
Thick & Thin penetration testing evaluates desktop applications for local and server-side weaknesses, uncovering flaws in binaries, memory, storage, and communications beyond standard web testing.
Adversarial Simulation
Uncover organizational weaknesses through Red Team, Purple Team, Social Engineering, Threat Emulation, & Threat Hunting.
Application Security
We provide rigorous penetration testing of your mobile apps, web apps, & thick clients, as well as API security testing & application security code review.
Cloud Security
Assess & protect your cloud data, applications, & infrastructure in all cloud environments, including AWS, Google Cloud, & Microsoft Azure.
Infrastructure Security
Identify critical network vulnerabilities through External/Internal Penetration Testing, PCI Penetration Testing, Wireless Penetration Testing, Cloud Security Assessment, & Remote Access Penetration Testing.
Device & IoT Security
Identify medical & embedded devices in an IoT-enabled environment & test critical hardware technologies to locate vulnerabilities & security-related issues.
Offensive Strategy
Utilize the years of experience & deep industry knowledge of our expert team of security consultants for AppSec Program Management & Developer Security Training.
How An In-Depth, Multi-Layered Penetration Testing Approach Works
Unlike other security firms, our Offensive Security Team extends our penetration testing protocols beyond the traditional means to provide in-depth, practical, & actionable insights through our unique three-phased Systematic Threat Evaluation Methodology (STEM).

Work With Our Pentesting Experts

Prioritize Based On Risk Level
Address vulnerabilities based on your reality and not on a best-guess approach that relies on lab-based prioritization. Get real information from seasoned experts.

Compliance? Of Course, We Do That!
Professional compliance experts have you in mind, so you don't have to worry about checking boxes. We will provide comprehensive help to make sure that your next audit is a success.

Identify Areas For Improvement
Receive practical and actionable insights into your existing security strategy and security investments. Is your investment in preventative technologies safeguarding your business or does it need to be fine-tuned?

Gain In-Depth Results
Obtain a real-world understanding of the risks that identified vulnerabilities actually pose. Built on industry-leading security methods— our process delivers results.
Red Team Simulation
Simulate real-world attacks to see how well your defenses, monitoring, and response hold up against advanced threats. Using stealth, social engineering, and technical tactics, testers mimic real attackers to find hidden gaps in detection, response, and overall security under realistic conditions.
Purple Team Simulation
Unite offensive and defensive teams in live attack simulations where red teams attempt exploits while blue teams detect and respond in real time, turning testing into a collaborative learning exercise that boosts visibility, strengthens detection, and accelerates overall security maturity.
Table Top Emulation
Discussion-based exercises where leaders and technical teams talk through how they would handle a simulated security incident. These sessions clarify roles, communication, and escalation steps without using live systems, and they expose gaps in planning and incident readiness before a real crisis occurs.
Definition:
An Internal Network Pen Test simulates an attack from within your organization’s internal environment. Compared to a standard pen test, which may include both internal and external components, this test focuses exclusively on systems and endpoints that are behind your firewall—accessible only to insiders or compromised internal users.
Who Needs It:
Organizations concerned about insider threats, unauthorized lateral movement, or weaknesses in internal segmentation. Common in regulated industries, companies with remote/hybrid employees, or those undergoing audits.
Definition:
This test targets your publicly exposed assets (like web servers, VPNs, email gateways) from the perspective of an external attacker. Unlike a full-scope pen test, it does not assess internal infrastructure but strictly evaluates internet-facing weaknesses.
Who Needs It:
Any company with a web presence, remote access services, or public applications. Especially important for businesses that manage sensitive customer data or handle online transactions.
Definition:
Application Pen Testing examines the security of a specific software application (web or mobile) by emulating real-world attacks. It goes deeper than standard pen tests by focusing on business logic flaws, session management, input validation, and authentication mechanisms.
Who Needs It:
Organizations developing or using web/mobile apps, particularly those handling personal, financial, or healthcare data. It’s also critical for compliance-driven sectors (PCI DSS, HIPAA, etc.).
Definition:
This test focuses specifically on Application Programming Interfaces (APIs), assessing how securely they expose data and services. While standard pen tests may touch on API endpoints, API Pen Testing dives deeper into authentication, data exposure, rate limiting, and input sanitization.
Who Needs It:
Businesses using APIs for mobile apps, third-party integrations, or internal microservices—especially those exposing APIs publicly or storing/transmitting sensitive data.
Definition:
Device & IoT penetration testing evaluates the security of connected devices and embedded systems, including firmware, hardware interfaces, communications, and backend services. It identifies weaknesses that could allow attackers to manipulate devices, extract data, or pivot deeper into your environment.
Who Needs It:
Organizations deploying IoT or connected devices in operational, customer-facing, or regulated environments—especially where devices collect, transmit, or control sensitive data or critical systems
Definition:
This testing targets desktop applications. Thick clients process data locally and communicate with servers (e.g., internal ERP apps), while thin clients depend on server-side processing (e.g., web-based apps). These tests go beyond typical web pen testing by analyzing local storage, memory, binaries, and communication protocols.
Who Needs It:
Companies running proprietary desktop applications, legacy systems, or specialized software in finance, healthcare, manufacturing, or critical infrastructure.
Learn From Our Offensive Security Experts Through Our Technical Blog

From Blind SSRF to RCE: How Source Code Review Exposed a Critical Exploit Chain

Java Class Exploitation in a Web Application Using Mozilla’s Rhino Library
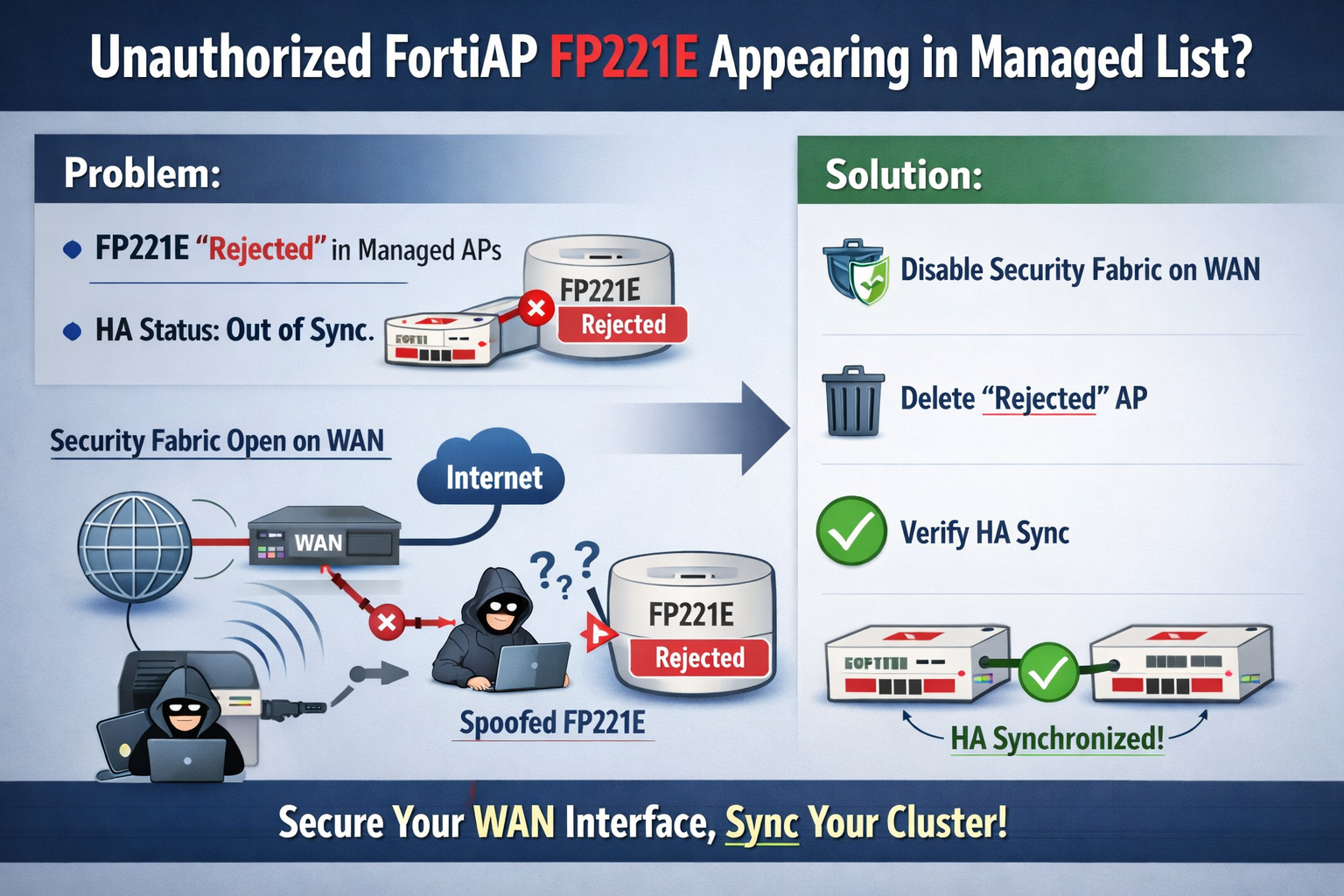
Technical Tip: Unauthorized FortiAP (FP221E) Unexpectedly Appearing in Managed List
Overview

